To ensure data security, deploy Creatio on-site as a web farm when installing the portal. Learn more about setting up a web farm in a separate article: Application server web farm.
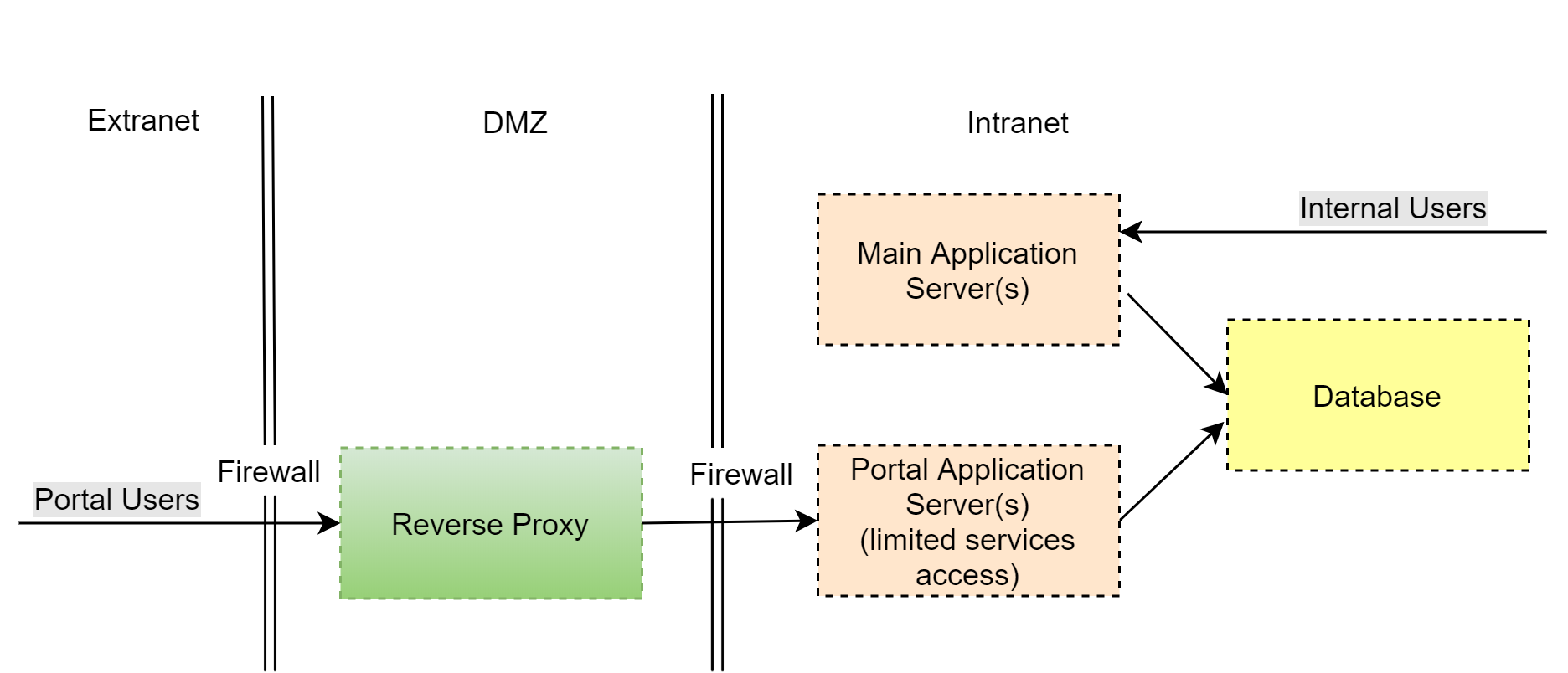
Set up the portal access as follows (Fig. 1):
-
-
Demilitarized zone (DMZ)
-
A reverse proxy server must be the only publicly accessible component in your DMZ.
-
The reverse proxy logs the primary network activity. You can also configure the proxy to restrict access to the configuration web services of your application.
-
Authorized portal users only have access to those configuration web services that they are expressly allowed to access on the application level.
-
Configure access permissions for new web services during the development process. Learn more in the developer documentation: Self-service portal.
-
-
-
Internal network (Intranet)
-
Deploy a separate set of application nodes on the web farm for servicing portal users. This set must not overlap with application nodes for servicing internal users.
-
To ensure the operation of the portal application and user application, create separate accounts that have different access permissions in the database.
-
Prohibit the login of system users in the portal application settings (disable “AuthProviders” except for portal users). To do this, make sure that the providerNames list in the web.config file of the application loader includes only SSPUserPassword:
This is required to ensure that only portal users can create sessions from an external network (Extranet).
-
Additionally, you can configure external authentication providers to add a second authorization step.
-
Deploy portal application nodes, DBMS, and user applications in separate segments with restricted access.
-